System Record Validation – 5879339052, Online Game bobfusdie7.9, About Tuzofalotaniz Calories, Tippaborough, 182.72.211.94

System record validation for 5879339052 and the online game bobfusdie7.9 examines cross-source reconciliation with Tuzofalotaniz Calories and Tippaborough references, anchored to IP 182.72.211.94. The approach emphasizes governance, standardized units, and auditable versioning to preserve provenance and integrity. It assesses validation of player IDs, game names, and usage metrics while ensuring privacy within interconnected data ecosystems. The framework invites scrutiny of anomaly detection and regional consistency, leaving a question of how these controls scale in practice as the discussion continues.
What Is System Record Validation for Multi-Source Data
System record validation for multi-source data is the systematic process of verifying that information originating from multiple inputs aligns and remains trustworthy as it moves through a data ecosystem. It emphasizes data governance, establishing standards, provenance, and traceability. Through cross source reconciliation, discrepancies are identified and resolved, ensuring consistency, accuracy, and reliability for informed decision making across diverse data streams.
Validating Player IDs, Game Names, and Usage Metrics
Are player IDs, game names, and usage metrics subject to validation across sources, and if so, how can their integrity be guaranteed? Validation employs cross-source reconciliation, canonicalization, and anomaly detection to ensure consistency. Mechanisms address invalid IDs and inconsistent calories, enforce provenance, and log changes for auditability, preserving trust while enabling freedom to explore data with confidence and precision.
Calorie Insights and Regional Data: Ensuring Consistency Across Profiles
Calorie insights and regional data require systematic alignment across profiles to maintain comparability and trust.
The examination emphasizes data normalization to harmonize disparate measurements and regional conventions, enabling accurate cross-profile comparisons.
By enforcing standardized units, definitions, and thresholds, researchers ensure profile consistency.
This disciplined approach supports reliable calorie insights and regional data interpretation without ambiguity or redundancy.
Security, Privacy, and Integrity in Interconnected Systems
How can interconnected systems maintain security, privacy, and integrity in complex, distributed environments? The discussion evaluates layered controls, authentication, and auditing to enforce privacy pitfalls avoidance while preserving usability. It presents integrity assurances through verification, versioning, and end-to-end validation. It acknowledges security tradeoffs, emphasizes data synchronization discipline, and recommends principled, auditable design to sustain trust across heterogeneous networks.
Frequently Asked Questions
How Is Cross-Domain Integrity Enforced During Data Synchronization?
Cross-domain integrity is enforced via verifiable data checks, cryptographic signatures, and versioned manifests during data synchronization. The process authenticates sources, validates hashes, and reconciles conflicts, ensuring consistency, traceability, and tamper-resistance across domains while preserving autonomy.
What Governance Models Govern Multi-Source Data Retention Policies?
Governance models govern multi-source data retention policies, emphasizing cross domain integrity and data synchronization. User consent and linked profiles shape retention boundaries, while anomaly communications and rollback mechanisms address validation failures for end users.
Can User Consent Impact Validation Across Linked Profiles?
Consent can influence validation across linked profiles by highlighting consent implications and profile linkage, enabling cross domain integrity and data synchronization within governance models; data retention and anomaly communications underpin user notifications, rollback mechanisms, and validation failures.
How Are Anomaly Detections Communicated to End Users?
An obstacle is that anomalies are communicated via clear alerts and dashboards. End users receive notifications with explanations of data privacy implications and model drift indicators, followed by recommended actions and ongoing monitoring details for informed responses.
What Rollback Mechanisms Exist After Validation Failures?
Rollback mechanisms exist to revert validated data states, ensure cross domain integrity enforcement, and restore data synchronization; governance models for multi source data, with user consent and linked profiles, mitigate anomaly detections while informing end users.
Conclusion
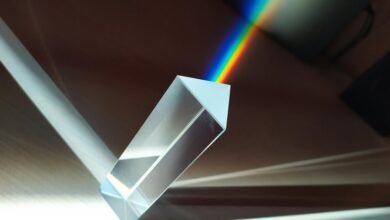
System record validation operates as a lattice of carefully joined prisms, each shard reflecting a distinct data source yet aligning toward a single truth. Through auditable versioning and end-to-end checks, patterns of player IDs, game names, and calorie metrics cohere like synchronized gears. In this interconnected landscape, privacy remains a quiet guardian, while integrity stands as a steady lighthouse. When changes ripple, provenance traces the wake, ensuring governance holds fast and anomalies are met with disciplined clarity.