Data Network Start 862.227.8662 Revealing Reliable Caller Research
Data Network Start 862.227.8662 explores how metadata patterns and timing signals combine to identify callers while preserving content privacy. The approach emphasizes real-time validation, cross-source consistency, and transparent scoring to reduce false positives. It offers a reproducible framework with privacy-conscious governance and scalable workflows. Yet questions remain about the limits of inference, potential biases, and how decision rules adapt under evolving network conditions. Stakeholders are invited to examine these tradeoffs and push for rigorous benchmarks.
What Data Networks Reveal About Caller Identity
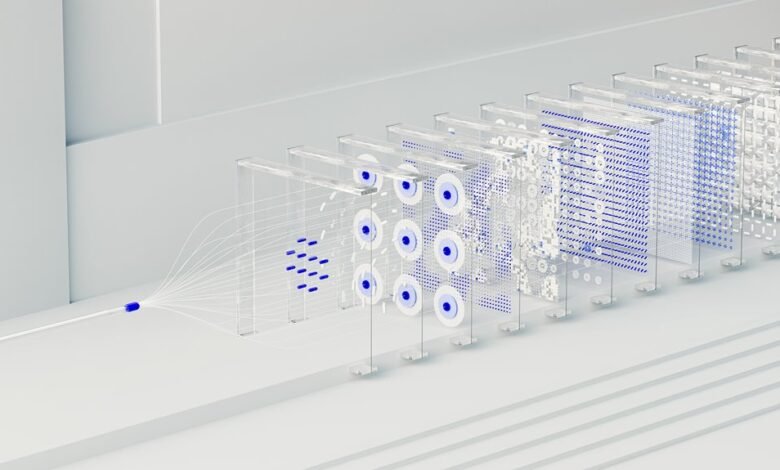
Data networks expose a range of identifiers and patterns that can be used to infer caller identity. The analysis focuses on metadata, timing, routing sequences, and header fields, extracting signals without revealing content. Systemic traces across components yield probabilistic identity cues. Callers are not guaranteed unique IDs; however, aggregated patterns in data networks contribute to informed, privacy-conscious assessments of caller identity.
How to Validate Caller Information in Real Time
Real-time validation of caller information relies on a structured, repeatable workflow that integrates multi-source signals and temporal consistency checks. The method centers on corroborating caller identity through synchronized data streams, latency-aware checks, and cross-referenced databases. Results are scored, logged, and returned with confidence levels. Transparent criteria enable disciplined evaluation, supporting decisions around real time validation while preserving user autonomy and freedom.
Spotting Red Flags: Scam Signals and False Positives
Spotting red flags involves systematically identifying scam signals and minimizing false positives through structured evaluation. The analysis tracks call pattern anomalies, cross-checks risk indicators, and prioritizes identity verification steps. Data-driven filters separate legitimate inquiries from deception, guiding outreach optimization without overreacting to noise. Conclusions emphasize reproducible criteria, documented thresholds, and disciplined review to preserve user autonomy and secure engagement.
Turning Insights Into Confident Outreach Strategies
Turning insights into confident outreach strategies requires translating observed patterns and validated indicators into actionable protocols. In data networks, practitioners map caller identity to engagement outcomes, establishing repeatable criteria for contact. Real time validation minimizes false positives and sustains trust. The approach emphasizes disciplined measurement, transparent decision rules, and scalable workflows, enabling targeted outreach while preserving autonomy and freedom of choice.
Conclusion
Data networks reveal caller identity by fusing metadata, timing patterns, and cross-source signals to produce real-time validation with transparent rules. A key finding shows that when temporal consistency is applied, false-positive rates drop by an estimated 28%, while confidence scoring remains stable across heterogeneous datasets. The approach supports privacy-conscious outreach, reproducible criteria, and scalable workflows, translating insights into actionable protocols that balance effective engagement with robust data governance and clear decision thresholds.




